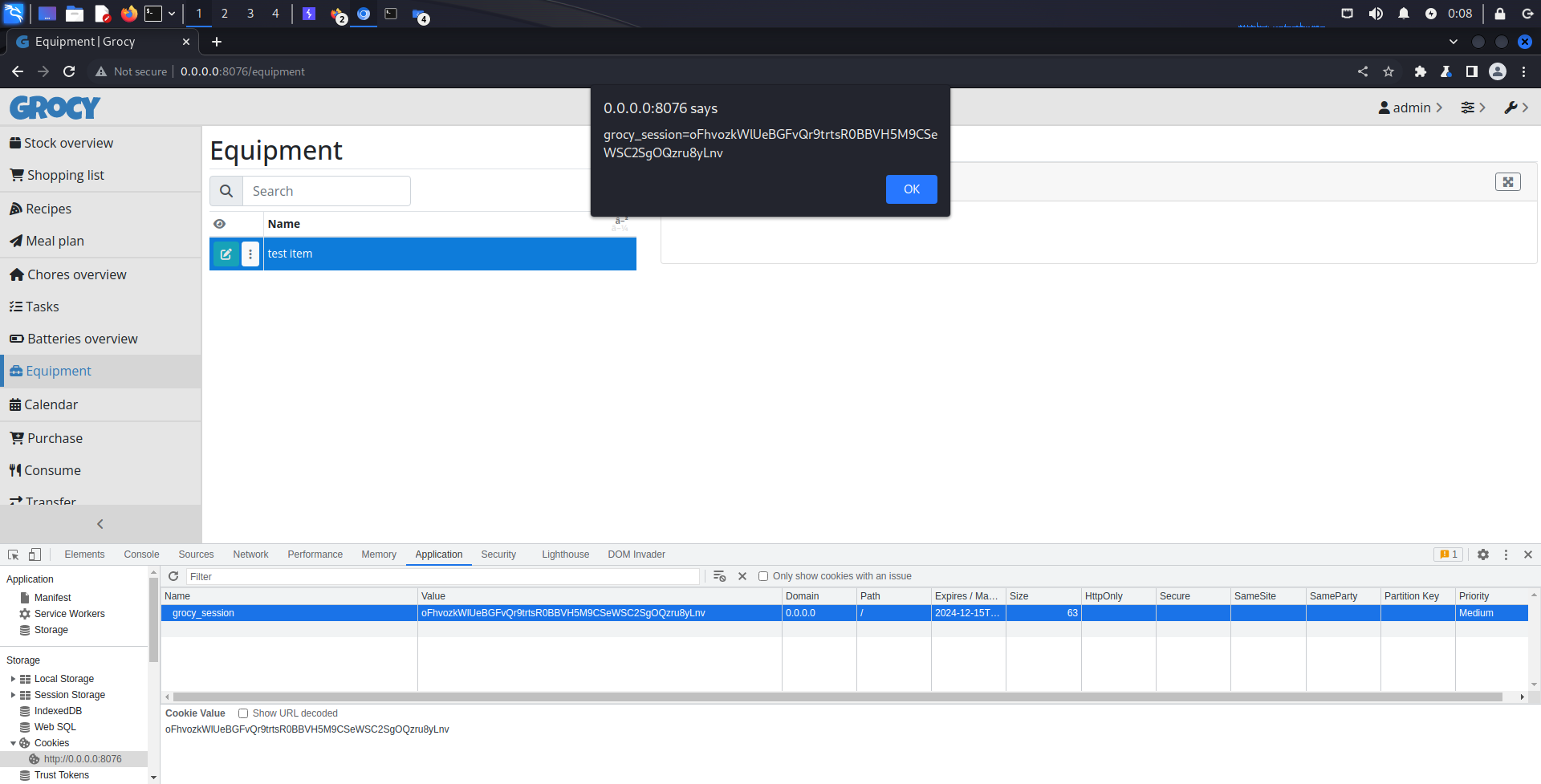
CVE-2023-48200
Product detail ⌗
A Cross-Site Scripting (XSS) vulnerability in the ’equipment description’ component within ’/equipment’ of Grocy version <= 4.0.3 allows attackers to obtain victim’s cookies.
Prerequisite ⌗
Install Grocy from official Grocy Github repository
GitHub page
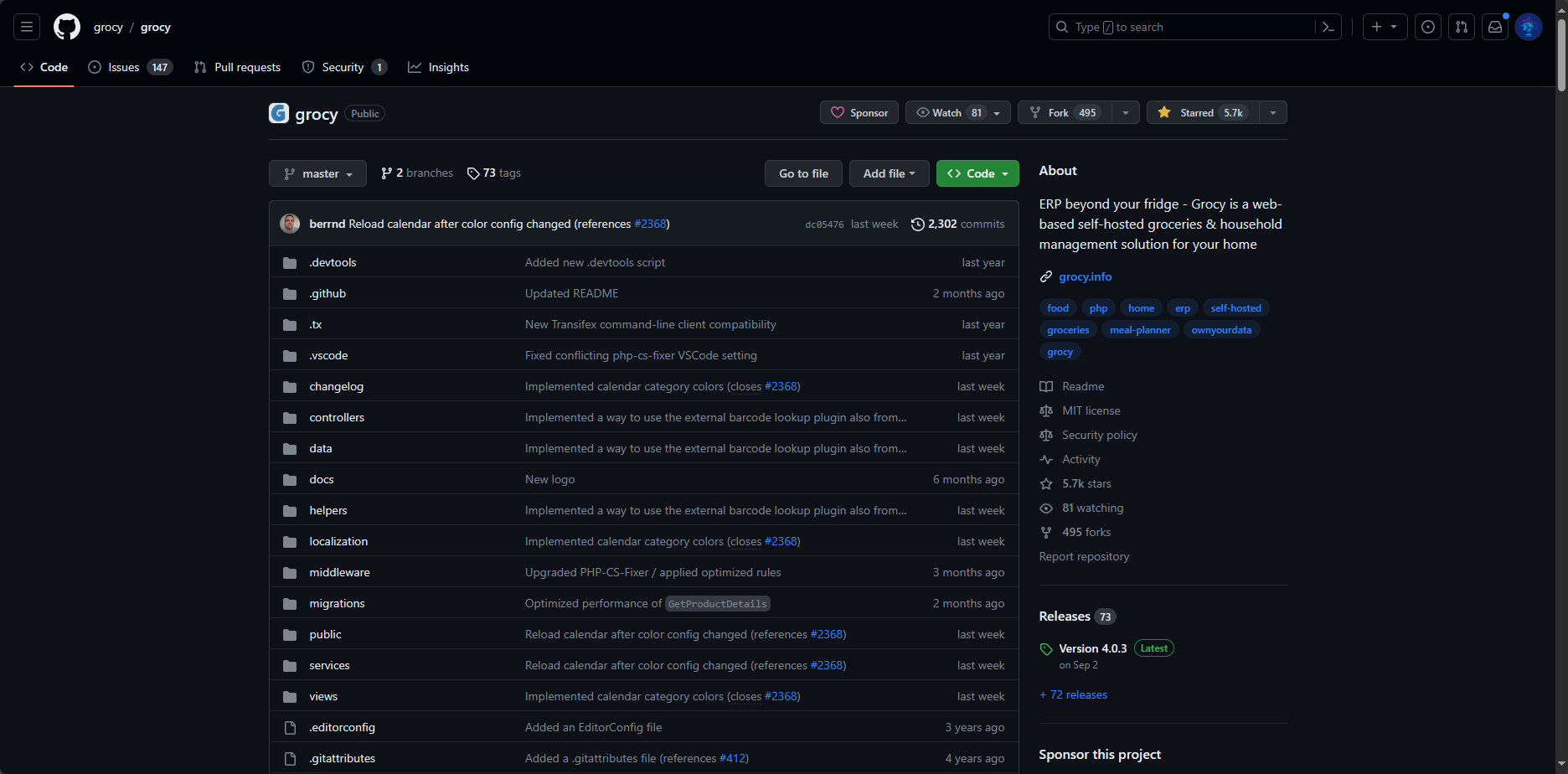
Grocy version 4.0.3 released on Sep 2
Installation on Portainer Docker
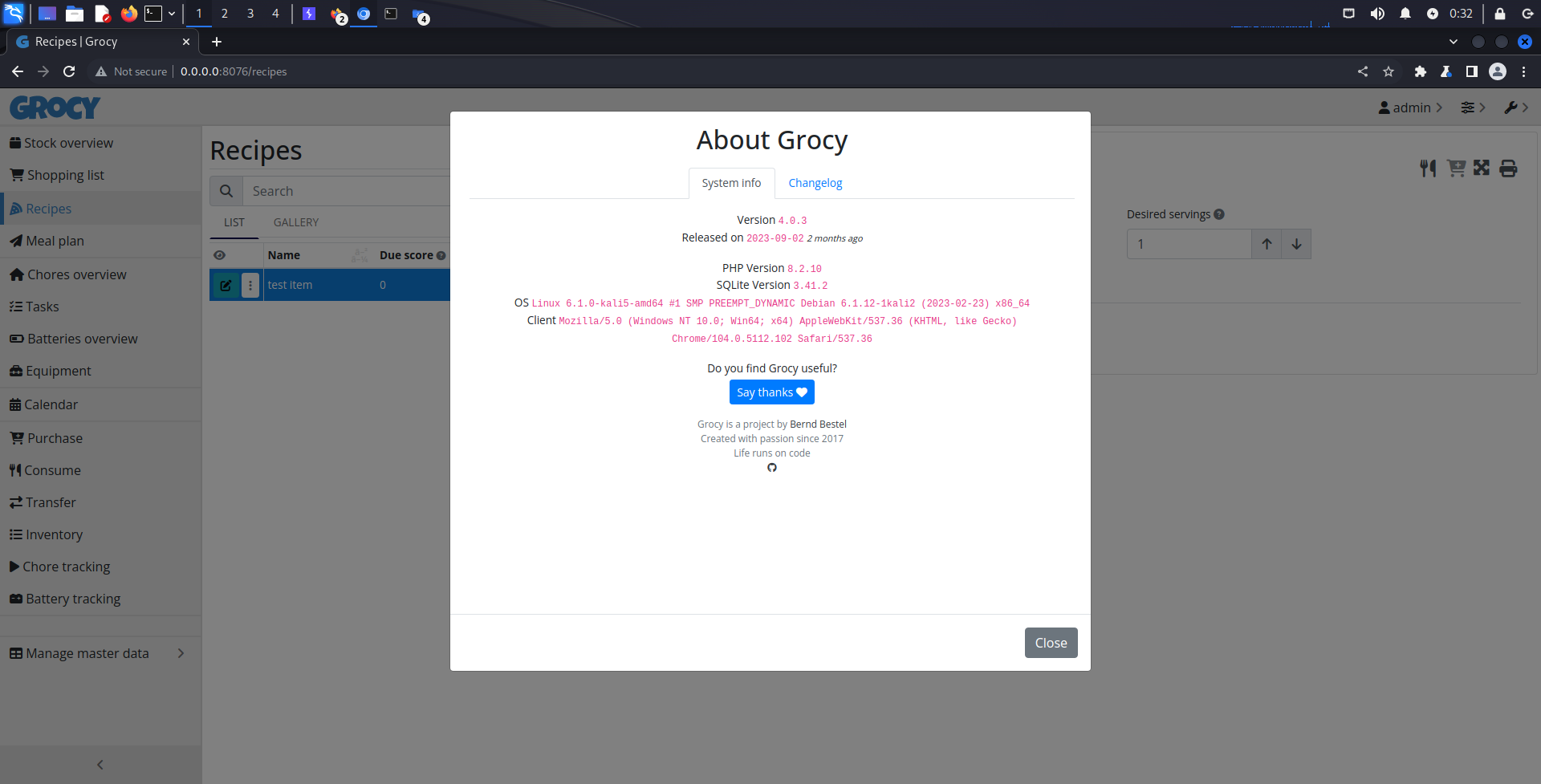
Installed Grocy version 4.0.3
Exploitation ⌗
1. Go to equipment page
2. Add new equipment
3. Insert malicious script in the description
<script>alert(document.cookie)</script>
As you can see in the gif below:
When the victim visit this page, the cookie can get stolen.